omg !! finally got kody maxson's picture and his document for court appearance
kill this belly kody
DO NOT REPOST WITHOUT GIVING CREDITS TO THE RIGHT PLACE
Saturday, October 20, 2012
Friday, October 19, 2012
Viper2323 another guy "involved" with Amanda Todd's photos
This summary is not available. Please
click here to view the post.
Amanda Todd's twitter+facebook profile and Kody Maxson's twitter+facebook
twitter - http://tinyurl.com/9ynmuyv (some tweets are being deleted)
facebook - http://tinyurl.com/9dyn95p (facebook account is deleted)
and so on i caught the bullies twitter profile
 here you go http://tinyurl.com/9n6338y (some tweets are being deleted)
here you go http://tinyurl.com/9n6338y (some tweets are being deleted)kody maxson's facebook - http://tinyurl.com/9nqpjjs (facebook account deleted)
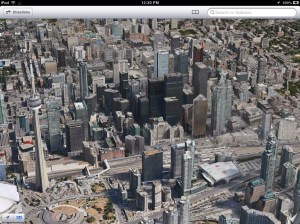
iOS 6 review
iOS 6 is here, and you’re probably in some stage of trying to download or install it on one or more device if you’re reading this, or at least contemplating an upgrade. Some might be thinking about hanging back, waiting to see if the changes result in a net gain or not. Well let me tell you upfront: this is an update that should please most, if not all, with the possible exception of a single area where growing pains are still apparent.
there are some elements of iOS 6 that quickly become features you’re not sure how you lived without, and those aren’t necessarily the ones that Apple spent a lot of time highlighting during past announcements and on their website. Here’s what I’ve enjoyed most about my experience with iOS 6.
1. New call response options. These seem silly and sort of minor, but in reality, the call experience on the iPhone is the one that that’s gone unchanged for longest. Any update is noteworthy, and one this useful is actually something to get excited about. You can set either custom messages or choose from Apple’s own and respond to incoming calls with an outgoing text or iMessage note, send calls to voicemail or ask for a reminder. This is a perfect example of Apple thinking about how people actually use their phones, and it’s a huge time saver that’s also considerate to people you’re desperately trying to ignore. Win win.

2. Do Not Disturb. I like my quiet time, but turning off notifications under iOS 5′s notification center was always a tricky affair, and I always missed some and then wouldn’t forget to put things back right again when I was through. Do Not Disturb fixes that, allowing you to easily schedule down time, complete with scheduling and sensible exceptions to keep you informed with what’s most important. This is another small but instrumental feature, and one you’ll find yourself using from day one.
3. VIP email inbox. Mail on iOS still feels a little bare compared to some of the complex setups you can create on the desktop with various tools, but this is a very nice addition to mobile mail that goes a long way toward making it more powerful. Assigning VIP status to your connections means that you’ll have quick access to your most important messages, making achieving total inbox zero less of a concern.
4. Shared Photo Stream. This one really should’ve debuted alongside iClout itself, but it’s good to have it now. Most times, the iPhone is the only camera I carry, and with improved camera features in iOS 6 and improved hardware on the iPhone 5 that’s likely to become even more true. So building sharing and commenting right into Photo Stream is a huge deal, and one that should benefit just about anyone.

3. VIP email inbox. Mail on iOS still feels a little bare compared to some of the complex setups you can create on the desktop with various tools, but this is a very nice addition to mobile mail that goes a long way toward making it more powerful. Assigning VIP status to your connections means that you’ll have quick access to your most important messages, making achieving total inbox zero less of a concern.
4. Shared Photo Stream. This one really should’ve debuted alongside iClout itself, but it’s good to have it now. Most times, the iPhone is the only camera I carry, and with improved camera features in iOS 6 and improved hardware on the iPhone 5 that’s likely to become even more true. So building sharing and commenting right into Photo Stream is a huge deal, and one that should benefit just about anyone.

5. Clock for iPad. You can mock me if you want, but I’ve never understood why the iPad didn’t offer a native clock app. Sure you could get third-party options, but an alarm on built-in system software just can’t be replaced by downloadable tools, at least in terms of peace of mind. The iPad Clock app also has some basic weather built in, so that’s an improvement, though it’s still missing the native dedicated weather app.
The Good
Some elements of iOS 6 seem promising, but either haven’t had the chance to prove their worth yet, or else just aren’t as useful as those things mentioned above in terms of day-to-day use. Here are highlights of features that fall into that category.
1. FaceTime over cellular. This is a welcome change, even ifAT&T isn’t being so welcoming about it. FaceTime has been Wi-Fi-only since its original debut, and that’s not exactly ideal for a video chat app designed to be used on mobile devices. FaceTime over cellular should increase its usefulness, but FaceTime in general still strikes me as a nice-to-have, not an essential service.
2. Siri improvements. Siri gets movie times and reviews, Yelp info and OpenTable reservations, app launching powers and the ability to post updates to Twitter and Facebook. Siri also expands to the new iPad, and the iPod touch (5th gen). Those are good things, and the service is clearly receiving much-needed attention from Apple’s engineering team, but I’m still not convinced that Siri’s found a daily place in most user’s lives. iOS 6 could help begin to change my mind on that front, however.

The Good
Some elements of iOS 6 seem promising, but either haven’t had the chance to prove their worth yet, or else just aren’t as useful as those things mentioned above in terms of day-to-day use. Here are highlights of features that fall into that category.
1. FaceTime over cellular. This is a welcome change, even ifAT&T isn’t being so welcoming about it. FaceTime has been Wi-Fi-only since its original debut, and that’s not exactly ideal for a video chat app designed to be used on mobile devices. FaceTime over cellular should increase its usefulness, but FaceTime in general still strikes me as a nice-to-have, not an essential service.
2. Siri improvements. Siri gets movie times and reviews, Yelp info and OpenTable reservations, app launching powers and the ability to post updates to Twitter and Facebook. Siri also expands to the new iPad, and the iPod touch (5th gen). Those are good things, and the service is clearly receiving much-needed attention from Apple’s engineering team, but I’m still not convinced that Siri’s found a daily place in most user’s lives. iOS 6 could help begin to change my mind on that front, however.

3. Passbook. If there’s a feature in iOS 6 that wins the award for most promising rookie, it’s Passbook. The virtual wallet app holds tickets, coupons, gift cards and more, and can pop up on your notification screen when you’re in the right place at the right time to use one. That’s a potentially powerful tool for marketers, retailers and brands of all stripes, and the interest from third-party companies either looking to help users create them (Passk.it, PassRocket and PassTools to name a few), or brands looking to take advantage (Eventbrite,Virgin, Starbucks, Amtrak, many more) suggests it’ll be everywhere pretty quickly. The only reason it qualifies as good and not the best is because we’ve yet to be able to test it in real world situations, which is the only place that counts.
4. Facebook integration. The addition of Facebook system-level sign on has been hinted at for a while now, and it’s nice now that it’s here. It makes sharing photos and posting status updates a lot easier. Third-party API access should help developers leverage it for interesting things, too, so overall this is a win for both users and Facebook.
5. Individual signatures for separate email accounts. This has long been an annoyance for iOS users, especially those who have both work and personal accounts on their devices. Now, you can set unique signatures for each email account on your device, ensuring that your boss won’t get the “<3″ emoticon – unless you really want them to.
The Not So Good
4. Facebook integration. The addition of Facebook system-level sign on has been hinted at for a while now, and it’s nice now that it’s here. It makes sharing photos and posting status updates a lot easier. Third-party API access should help developers leverage it for interesting things, too, so overall this is a win for both users and Facebook.
5. Individual signatures for separate email accounts. This has long been an annoyance for iOS users, especially those who have both work and personal accounts on their devices. Now, you can set unique signatures for each email account on your device, ensuring that your boss won’t get the “<3″ emoticon – unless you really want them to.
The Not So Good
1. Maps. This is pretty much a known weakness of iOS 6 at this point, but it’s going to affect those who depend on public transit most of all. Walking and driving directions are actually still pretty solid in Apple’s Maps offering, and turn-by-turn navigation works well, albeit at a heavy cost to battery (generally standalone GPS units spend most of their lives plugged in, so this isn’t a huge deal). There are reportedly third-party apps on the way to shore up the gap in public transit, and Yelp points-of-interest are useful, but for users coming from Google Maps (lack of street view hurts as much as anything else) either on iOS, or worse, on Android devices, it’s going to be a step back.
2. Redesigned App Stores. All of the App Stores on all iOS 6 devices got a visual facelift, along with some changes in Genius and search results inherited from acquired app discovery company Chomp. The aesthetics are nice; things look a lot better all around, versus the somewhat stale older design, and there are functional advantages like not having to type in your password to install updates. But the search results, which come up one at a time on iPhone and four at a time on iPad, are not a step forward for discovery. I can see the logic: present one good result with ample context as to why it was returned, with the idea being that quality beats volume. But in practice, it makes looking for apps with some, but not an exact idea of what you’re looking for, more difficult.
Overall, iOS 6 is a big step forward, but that’s hardly surprising given Apple’s track record. As always, there will be those who say it doesn’t push the envelope enough, and Maps has already ruffled quite a few feathers. But that Maps has raised such an outcry is perfect example of why Apple’s generally doing things right with iOS updates: it stick out like a sore thumb, and in truth, it’s not a big enough step backward to do anything beyond mildly inconvenience a few folks. Plus, it’s inevitable that Google will offer up its own standalone Maps app to address that single deficiency. So, in other words, what are you waiting for? Go get that update.
source
2. Redesigned App Stores. All of the App Stores on all iOS 6 devices got a visual facelift, along with some changes in Genius and search results inherited from acquired app discovery company Chomp. The aesthetics are nice; things look a lot better all around, versus the somewhat stale older design, and there are functional advantages like not having to type in your password to install updates. But the search results, which come up one at a time on iPhone and four at a time on iPad, are not a step forward for discovery. I can see the logic: present one good result with ample context as to why it was returned, with the idea being that quality beats volume. But in practice, it makes looking for apps with some, but not an exact idea of what you’re looking for, more difficult.
Overall, iOS 6 is a big step forward, but that’s hardly surprising given Apple’s track record. As always, there will be those who say it doesn’t push the envelope enough, and Maps has already ruffled quite a few feathers. But that Maps has raised such an outcry is perfect example of why Apple’s generally doing things right with iOS updates: it stick out like a sore thumb, and in truth, it’s not a big enough step backward to do anything beyond mildly inconvenience a few folks. Plus, it’s inevitable that Google will offer up its own standalone Maps app to address that single deficiency. So, in other words, what are you waiting for? Go get that update.
source
Google Maps ‘App’ on iOS 6 Isn’t Great Either

I lost all patience with Apple’s Maps app when it directed me to the middle of a state park when it should have been taking me home.
The turn-by-turn directions, supposedly the saving grace of the troubled iOS 6 Maps app, work wonderfully — but they’re only as good as the information you put in them. And Maps, in conjunction with Siri, had decided “home” was in a park with the same name as my street, six miles away. (Bafflingly, it got the directions right on the second try.)
Thursday, October 18, 2012
Anonymous Hacker group have tracked down the sex-obsessed cyberbully who drove a 15-year-old girl (Amanda Todd) to suicide

Hacker group Anonymous may have tracked down the sex-obsessed cyberbully who drove a 15-year-old girl to kill herself last week. Today Anonymous posted a video on YouTube naming a 32-year-old man from British Columbia, as the person responsible for the October 10th suicide of 15-year-old Amanda Todd. Anonymous has started #OpRIP to hunt down those who bullied Todd.
Wednesday, October 17, 2012
AdSense for feeds is going away on december 5th
"After carefully evaluating the product, we’ve decided to retire the AdSense for feeds product.
The process will happen in two phases and your account will be affected, depending on your usage of the product. To check whether you’re currently generating any revenue from AdSense for feeds, run your “Products” performance report and review the listed products for recent data for "AdSense for feeds."
Although AdSense for feeds is going away, this change won’t affect any other AdSense products you’re currently using or the availability of the other products to you.
Payments
Your AdSense for feeds units will continue to accrue earnings until December 3, when they will stop showing ads on your RSS feeds. As of the last day of December 2012, your earnings will be finalized as usual. At this point, one of the following will apply:
If your earnings exceed the payment threshold, your account will be sent for approval for payment, and payments will be issued through the standard AdSense payment process.
If your earnings do not exceed the payment threshold, but you use other AdSense products, your AdSense for feeds earnings will be accrued toward payment in a future period when your AdSense account does exceed the payment threshold.
If your earnings do not exceed the payment threshold and you don’t use other AdSense products then the amount of accrued earnings from your AdSense for feeds units will remain as a balance in your AdSense account for as long as your account is open.
Reports and earnings
Reporting on AdSense for feeds and corresponding channels will remain available in your account. Even though you will no longer be able to access AdSense for feeds settings and channels, you will be able to see historical performance of them on thePerformance reports tab in your AdSense account."
Sunday, September 23, 2012
Sensitive data in human brain successfully extract by Hackers
It is now possible to hack the human brain ? YES ! This was explained
researchers at the Usenix Conference on Security, held from 8 to 10
August in Washington State. Using a commercial off-the-shelf
brain-computer interface, the researchers have shown that it’s possible
to hack your brain, forcing you to reveal information that you’d rather
keep secret.
In a study of 28 subjects
wearing brain-machine interface devices built by companies like Neurosky
and Emotiv and marketed to consumers for gaming and attention
exercises, the researchers found they were able to extract hints
directly from the electrical signals of the test subjects’ brains that
partially revealed private information like the location of their homes,
faces they recognized and even their credit card PINs.
Brain-computer interface or BCIs
are generally used in a medical setting with very expensive equipment,
but in the last few years cheaper, commercial offerings have emerged.
For $200-300, you can buy an Emotive or Neurosky BCI, go through a short
training process, and begin mind controlling your computer.
“These devices have access
to your raw EEG [electroencephalography, or electrical brain signal]
data, and that contains certain neurological phenomena triggered by
subconscious activities,” says Ivan Martinovic, a member of the faculty in the department of computer science at Oxford.
“So the central question we were asking with this is work was, is this is a privacy threat?” To
extract this information, the researchers rely on what’s known as the
P300 response a very specific brainwave pattern that occurs when you
recognize something that is meaningful, or when you recognize something
that fits your current task. The researchers basically designed a
program that flashes up pictures of maps, banks, and card PINs, and
makes a note every time your brain experiences a P300.
The researchers found they could
guess which of those random numbers was the first digit in the PIN with
about 30% accuracy on the first try–far from a home run, but a
significantly higher success rate than a random guess.
This brain hack can only improve in efficacy as BCIs become cheaper, more accurate, and thus more extensively used. “But social engineering could make that possible. Attackers are creative.” What do you thing about a Brain Malware ?
Tuesday, August 21, 2012
Julian Assange - The most Fuckable Man on the Planet
Julian Assange made a speech today from the balcony of the Ecuadorian Embassy in London and I felt a primal urge brought on by the fact that this man, in all his manly glory, has stuck his proverbial neck out for the essence of life. Truth and Justice. He is a handsome and articulate man, fighting for the basic rights of every human being on the planet. What could be more sexy? Putting aside husbands, lovers, friends, and professional media, he can Wik my Leaks anytime he wants.
Julian started by reminding us that he is there because he can’t be elsewhere. He blended his thanks for Ecuador’s stand for justice with the announcement of an emergency meeting of Latin American countries next Friday specifically to address his situation and to defend the right of asylum.
He made a straight forward statement that the United States must return to the values it was founded on and “Obama must do the right thing.” Bradley Manning must be released and “he is a hero and example to all of us…..” He gave us a grim reminder that Bradley Manning has been held for 815 days and by law you can only be held 120 days without a trial.
Julian ended his short speech with the statement, “There is unity in oppression. There must be unity in response.”
 That said, we need a “pussy riot” of the colossal type. It is time for all you Princesses and Queens of revolution to step up and take the reigns and show Obama and David Cameron that women live true to the old adage, “hell has no fury like a woman scorned.” And, scorned we have been. The entire planet has been scorned and it is time to show more fury than has ever been displayed that we, want and deserve, the truth.
That said, we need a “pussy riot” of the colossal type. It is time for all you Princesses and Queens of revolution to step up and take the reigns and show Obama and David Cameron that women live true to the old adage, “hell has no fury like a woman scorned.” And, scorned we have been. The entire planet has been scorned and it is time to show more fury than has ever been displayed that we, want and deserve, the truth.Women, with all their motherly graces can and should do what we do best. Raise up our voices, heat up the keyboards, and let the world know we have had enough and we are taking control. Let Julian Assange go to Ecuador peacefully and rightfully. Leave him alone to live his life and continue to protect us through the simple act of providing the truth.
Man or woman, you can’t really live without the truth. Your government is obligated to inform you and support you in a healthy and violence free life. We have had enough of secrets, lies and false flags. We have had enough of war and economic strife. It is time ladies (and gentlemen) to take back our Mother Earth.
Here are the emails to Obama, Cameron and the President of Ecuador. Write them now, and tell them Ann Smith sent you. I’ll write too, after my cold shower.
- http://www.whitehouse.gov/contact/submit-questions-and-comments
- http://www.davidcameron.com/2007/06/contact-david-cameron.html
- http://www.facebook.com/pages/RAFAEL-VICENTE-CORREA-DELGADO/197563636932502
The goal is justice, the method is transparency. It's important not to confuse the goal and the method.
Written By : Ann Smith (Executive Editor) is the irreverent Executive Editor of The Hacker News, you can reach her at: http://www.facebook.com/ann.smith.92102
AMD Blog Hacked, Database leaked on Internet
A team of Hackers called, "r00tBeer Security Team" today hack into official blog of Advanced Micro Devices (AMD) which is a American multinational semiconductor company. AMD is the second-largest global supplier of microprocessors based on the x86 architecture and also one of the largest suppliers of graphics processing units.
Hacker deface the blog page (http://blogs.amd.com/wp-content/r00tbeer.html) and also leak the complete user database of blog on his twitter account. Leaked database SQL file uploaded on Mediafire by Hackers which include 200 AMD user's Emails, Wordpress Blog Usernames and Passwords.
During the time of writing, I think AMD is not aware about that they are the Victim of a Hack attack. We are tweeting to the AMD team for informing them. Screenshot of Hack as shown below:
Now only AMD, these hackers also hack another High Profile website called "TBN - The Botting Network", A Popular forum to learn How to make Money with 96000 members was got hacked and Complete database was also leaked via Hackers Twitter Account.
Serious Security Flaw : iPhone Bug Allows SMS Spoofing
A rather serious security flaw in the iPhone’s SMS messaging system has been discovered and revealed by well-known security researcher and jailbreak extraordinaire ‘pod2g’. Security flaw affecting all iPhones that he says could facilitate hackers or thieves to access your personal information.
The researcher claims that the flaw has actually been present in Apple’s iPhone software ever since the first iPhone was launched in 2007, but has failed to have been picked up on by anybody, including Apple it seems.
Researcher revealed an SMS spoofing flaw that affects every version of Apple’s mobile OS. Using the flaw, hackers could spoof their identities via text and send messages asking for private information (by pretending to be from a users’ bank, for example), or direct users to phishing sites.
Users would be under the impression they were replying to the sender displayed on the screen of their iPhone, when in fact the text would be routed through to a different number without their knowledge.
pod2g highlights several ways in which malicious parties could take advantage of this flaw, including phishing attempts linking users to sites collecting personal information or spoofing messages for the purposes of creating false evidence or gaining a recipient's trust to enable further nefarious action.
“…In the text payload, a section called UDH (User Data Header) is optional but defines a lot of advanced features not all mobiles are compatible with. One of these options enables the user to change the reply address of the text. If the destination mobile is compatible with it, and if the receiver tries to answer the text, he will not respond to the original number, but to the specified one.”
In many cases the malicious party would need to know the name and number of a trusted contact of the recipient in order for their efforts to be effective, but the phishing example shows how malicious parties could cast broad nets hoping to snare users by pretending to be a common bank or other institution.
In the meantime be prepared to update your iOS version as new options become available, as exploits are discovered Apple typically works quickly to fix those issue whenever possible.
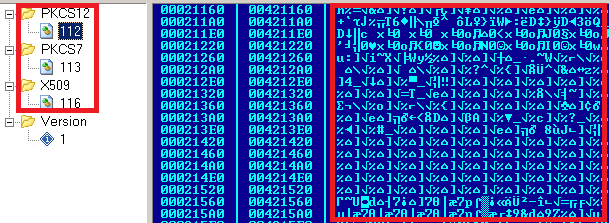
Shamoon Malware : Permanently wiping data from Energy Industry Computers
Malware researchers have uncovered an attack targeting an organization in the energy industry that attempts to wreak havoc by permanently wiping data from an infected computer's hard drive and rendering the machine unusable. Symantec would not name the victimized firm, and so far has seen the attack only in this one organization.
W32.Disttrack is a new threat that is being used in specific targeted attacks against at least one organization in the energy sector. It is a destructive malware that corrupts files on a compromised computer and overwrites the MBR (Master Boot Record) in an effort to render a computer unusable.
W32.Disttrack consists of several components:
- Dropper—the main component and source of the original infection. It drops a number of other modules.
- Wiper—this module is responsible for the destructive functionality of the threat.
- Reporter—this module is responsible for reporting infection information back to the attacker.
"Ten years ago we used to see purely malicious threats like this," muses Symantec researcher Liam O Murchu. The likely scenario for the victim would be an experience in which the computer is booting up, but all the files get erased, and the computer collapses into a non-bootable state.
Saudi Arabia-based Saudi Aramco, the world’s largest crude exporter, was reportedly hit by a computer virus this week that entered its network through personal computers. Shamoon is unusual because it goes to great lengths to ensure destroyed data can never be recovered, something that is rarely seen in targeted attacks. It has self-propagation capabilities that allow it to spread from computer to computer using shared network disks. It overwrites disks with a small portion of a JPEG image found on the Internet.
twitter Subscribe for latest Updates Your Friend can help Investigators to Access your Facebook Profile
If you’re not already particularly picky about who you friend on Facebook, you might want to think about rejiggering those privacy settings. It's not the backdoor access that the FBI has been pushing for, but US District Judge William Pauley III has now ruled that it and other law enforcement agencies are entitled to view your Facebook profile if one of your "friends" gives them permission to do so.
As GigaOm reports, a New York City federal judge ruled in a recent racketeering trial that it’s legal for police to view your Facebook profile if one of your friends grants them permission. Better start sniffing out the rats on your friends list.
That’s because all of that data that you think is personal really isn’t that personal after all, according to the Judge. "Colon’s legitimate expectation of privacy ended when he disseminated posts to his friends because those friends were free to use the information however the wanted including sharing it with the Government."
Both government agencies and private companies alike are mining social media to gain additional knowledge. Whether it’s a criminal investigation like this one or insurance companies reportedly combing through Facebook profiles to determine the party at fault in an auto accident, the freedom and public nature of social media can work both for and against its users.
Ultimately, users have to be aware of the public status of online information as well as the ease with which it can be obtained. Don’t post anything you don’t want to be found or seen.
Security Firm Reveals Flaw in Dirt Jumper Bot
A team of researchers has discovered a weakness in the command-and-control infrastructure of one of the major DDoS toolkits, Dirt Jumper, that enables them to stop attacks that are in progress.
The command and control (C&C) servers of the Dirt Jumper DDoS toolkit can be compromised and, in principle, completely taken over via SQL injection holes.
SQL injection involves inserting database instructions in unexpected and unprotected places, effectively taking charge of a web application's database from the outside. According to the Prolexic report, the open source penetration testing tool sqlmap can be used to dump the contents of Dirt Jumper's database configuration file in a matter of seconds, revealing administrative usernames and passwords.
The company's research includes Dirt Jumper v.3, Pandora and Di BoT. According to Prolexic, the Dirt Jumper family of DDoS botnet kits was originally authored by an individual who uses the handle ‘sokol.’ Various versions of Dirt Jumper were sold privately and leaked to the public.
"DDoS attackers take pride in finding and exploiting weaknesses in the architecture and code of their targets. With this vulnerability report, we've turned the tables and exposed crucial weaknesses in their own tools," said Prolexic's CEO, Scott Hammack.
Pandora can be used to launch five different attack types, including a combination of techniques against the web application and infrastructure layers of targeted websites. Dirt Jumper seems to have overtaken rivals to become one of the most successful DDoS toolkits available on the Russian underground.
"Construction of a new variant of Dirt Jumper is relatively easy, only requiring basic knowledge of Delphi, a basic understanding of PHP and MySQL, and U.S. $5,000 to purchase the Dirt Jumper builder source code".
Google engineers Warn Of Serious Unpatched Adobe Reader Flaws
Adobe has missed dozens of vulnerabilities in Reader in this week’s Patch Tuesday run according to Google engineers who reported the flaws. Sixteen vulnerabilities still affected the Windows and Mac OS X versions, while 31 critical and “trivially exploitable” bugs were found in the Linux application.
Of particular concern to Google’s Mateusz Jurczyk and Gynvael Coldwind are bugs in Reader for Linux, although other issues affect versions for Windows and OS X. For the Linux version, which went completely unpatched, Adobe and Google have been working together to counter 14 “new unique crashes” and nine “test-cases” that were potentially exploitable for remote code execution.
When Adobe released a new version of Reader for Windows and Mac OS X earlier this week, it patched 12 vulnerabilities, but another 16 remained unpatched. Jurczyk and Coldwind decided to come forward with information on those flaws in the interest of user safety, as Adobe has no plans to issue additional out of band updates before 27 August.
“Considering that fixing the first twenty four crashes took twelve unique code fixes, it is expected that the remaining crashes might represent around eight more unique problems. Adobe plans to fix these remaining bugs and issue an update for the Linux version of Reader in an upcoming release,” the Google researchers said.
Adobe released new versions of Adobe Acrobat, Reader, Shockwave, and Flash to patch security holes in those products as well.
Check out the details of the Microsoft and Adobe security bulletins to figure out which ones apply to you, and prioritize the patches that are most critical or have the greatest potential to impact your PCs.
MyAgent Trojan Targets Defense and Aerospace Industries
FireEye Security experts are analyzing a targeted trojan that leverages emailed PDF files to gain access to systems and deliver its payload to specified networks in the aerospace, chemical, defense and tech industries.
"We have seen different versions of this malware arriving as an exe inside a zipped file or as a PDF attachment. In this particular sample, the exe once executed opens up a PDF file called "Health Insurance and Welfare Policy." In addition to opening up a PDF file, the initial exe also drops another executable called ABODE32.exe (notice the typo) in the temp directory."
 The malware also uses JavaScript to assess which version of Adobe Reader is currently running on the host machine, and then executes attacks based on known vulnerabilities in the discovered version. Once the trojan has infected its host machine, it communicates with its command and control server, the user agent string and URI of which are hard-coded into MyAgent’s binary.
The malware also uses JavaScript to assess which version of Adobe Reader is currently running on the host machine, and then executes attacks based on known vulnerabilities in the discovered version. Once the trojan has infected its host machine, it communicates with its command and control server, the user agent string and URI of which are hard-coded into MyAgent’s binary.FireEye reports that most of the payloads are detected by updated antivirus software, based on research executed by running the binaries through VirusTotal.
Bafruz trojan vs Microsoft : Malicious Software Removal Tool Updated
There's a new family of malware that's using a complex set of capabilities to disable antimalware and listen in on sessions between users and some social networks. Bafruz is essentially a backdoor trojan that also is creating a peer-to-peer network of infected computers.
Microsoft has announced that its Microsoft Malicious Software Removal Tool has recently been modified to detect two new malware families, Matsnu and Bafruz.
The payload seems to start by terminating a long list of security processes listed in its code. It then displays a fake system alert that looks like that of any standard rogue AV attack.
The device actually restarts in Safe Mode. Here, the malware can disable all the security products more easily, allowing it to perform its other tasks without being interrupted.
"This may lead the user into believing all is well with their security product, while in the meantime, Bafruz is downloading additional components and malware onto the computer in the background through its P2P network," Microsoft.
Microsoft has now added Bafruz to the list of threats detected by its Malicious Software Removal Tool.The update came Tuesday, along with nine patches for 26 security vulnerabilities.
Airport VPN hacked using Citadel malware
It sounds like an air traveler’s nightmare, Researchers at Trusteer recently uncovered a variant of the Citadel Trojan targeting the virtual private network (VPN) credentials used by employees at a major airport.The firm would not disclose the name of the airport because the situation is being investigated by law enforcement.
Many businesses use VPNs to provide outside workers with access to secure data. Incursions on these networks often involve advanced “Man in the Browser” malware such as the Citadel, Zeus, and SpyEye programs. The man-in-the-browser (MITB) assault first used form-grabbing malware, which steals data entered into web forms before it is passed over the internet, to steal the airport employees' VPN usernames and passwords, Amit Klein, Trusteer's chief technology officer, said in a blog post.
“This was potentially very dangerous, but we don’t know whether the attacker group was targeting the financial system of the airport for economic gain or if the attack was terrorism-related,”
The airport VPN was immediately disconnected after officials there were made aware of the breach and authorities are investigating.
The product that the airport was using to provide strong authentication for employees gave each user two choices: log in with a username and a one-time password that's sent via SMS or a smartphone app; or log in using a CAPTCHA-like image of 10 digits that the user maps to his own static password. The Citadel malware used the screen-capture tactic to defeat this.
"This security measure prevents the form grabber from capturing the actual static password. This is where the screen capturing feature in Citadel kicks in," Klein said.
Trusteer doesn't know who the attackers are and what they are after, but Kedem says they could be trying to gather intelligence on airport security processes, or even the border customs service.He says the attack appears to be very targeted, and the bottom line is that VPN connections are not safe.
In addition to using endpoint cybercrime prevention software, Kedem also advises users to abide by standard practices for preventing infection: avoid opening unknown attachments or clicking links in emails.
BackTrack 5 R3 Released - Download Now !
The latest version of Backtrack is out! Check out Backtrack 5 R3!
“The time has come to refresh our security tool arsenal – BackTrack 5 R3 has been released. R3 focuses on bug-fixes as well as the addition of over 60 new tools – several of which were released in BlackHat and Defcon 2012. A whole new tool category was populated – “Physical Exploitation”, which now includes tools such as the Arduino IDE and libraries, as well as the Kautilya Teensy payload collection.”
Backtrack Team have released a single VMware Image (Gnome, 32 bit), for those requiring other VM flavors of BackTrack.
Download BackTrack 5 R3
FinFisher spyware found running on computers all over the world
FinFisher, a software application used by law enforcement agencies for surveillance, appears to be far more widespred than originally thought.Sold by British company Gamma Internationl Gmbh, FinFisher secretly monitors computers by turning on webcams, recording everything the user types with a keylogger, and monitoring Skype calls.
It can also bypass popular antivirus products, communicate covertly with remote servers, record emails, chats, and VOIP calls, and harvesting data from the hard drive.
On Wednesday, computer security company Rapid7 researcher Claudio Guarnieri shared new details of the workings of FinFisher, a piece of malware sold by UK contractor Gamma Group to government agencies. He found FinFisher servers at work in Australia, Czech Republic, United Arab Emirates, Ethiopia, Estonia, Indonesia, Latvia, Mongolia, Qatar, and the United States.
Rapid7 has published the IP addresses and communication "fingerprint" of the command and control servers it has discovered. The information can be used in intrusion detection systems. "If you can identify those networks actually communicating with those IPs, it most likely means some of the people on those networks are being spied on in some way," Guarnieri said.
Muench, who is based in Munich, has said his company didn’t sell FinFisher spyware to Bahrain. He said he’s investigating whether the samples used against Bahraini activists were stolen demonstration copies or were sold via a third party.
Researchers uncover security holes in China-based Huawei routers
Routers made by China-based Huawei Technologies have very few modern security protections and easy-to-find vulnerabilities, two network-security experts stated at the Defcon hacking convention.
Huawei is one of the fastest-growing network and telecommunications equipment makers in the world. The vulnerabilities were discovered and presented by Felix Lindner and Gregor Kopf of the security firm Recurity Labs. They talks about three vulnerabilities demonstrated at the Defcon conference, which included a session hijack, a heap overflow, and a stack overflow, and the discussion of more than 10,000 calls in the firmware code that went to sprintf, an insecure function.
The problem is due to the use of "1990s-style code" in the firmware of some Huawei VRP routers, he said. (The models are the Huawei AR18 and AR 29 series). With a known exploit, an attacker could get access to the systems, log in as administrator, change the admin passwords and reconfigure the systems, which would allow for interception of all the traffic running through the routers.
Both Lindner and Kopf have criticized Huawei for not having a security contact, as well as for its lack of security advisories for its products. Additionally, the researchers say firmware updates don't talk about bugs that may have been fixed.
A U.S.-based Huawei representative provided CNET with the following statement:
We are aware of the media reports on security vulnerabilities in some small Huawei routers and are verifying these claims. Huawei adopts rigorous security strategies and policies to protect the network security of our customers and abides by industry standards and best practices in security risk and incident management. Huawei has established a robust response system to address product security gaps and vulnerabilities, working with our customers to immediately develop contingency plans for all identified security risks, and to resolve any incidents in the shortest possible time. In the interests of customer security, Huawei also calls on the industry to promptly report all product security risks to the solutions provider so that the vendor's CERT team can work with the relevant parties to develop a solution and roll-out schedule.
Anonymous hackers target Australian Intelligence and ASIO websites
Hacking group Anonymous claimed to have shut down a computer server belonging to Australia's domestic spy agency ASIO, reportedly briefly closing down access to its public web page. The Australian Security Intelligence Organization acknowledged some disruption to its website.
The ASIO website was down for about 30 minutes after the attack and is now operating slowly or not at all. It appears the attack may be ongoing, but ASIO’s technical staff are recovering the situation.
Anonymous has been claiming on its Twitter feed over the past few days that it was able to bring down several sites, including ASIO's. It wrote: "asio.gov.au has been down for some time now, And will be for the rest of the day!"
It appeared linked to a controversial government plan to store the web history of all Australians for up to two years which was shelved Thursday until after the 2013 elections.
The group Anonymous, which is believed to be a loosely affiliated network of “hacktivists”, has attacked sites around the world including those of MasterCard and Visa, the US Justice Department, and the Tunisian and Yemen governments.
In 2011, ASIO revealed it had established a cyber intelligence unit although it is believed to have been operating for some time before it was announced.
Kaspersky Labs uncover 'Gauss' Espionage Malware hits Middle East banks
A new cyber surveillance virus has been found in the Middle East that can spy on banking transactions and steal login and passwords, according Kaspersky Lab, a leading computer security firm.
After Stuxnet, Duqu, and Flame, this one seems to mainly spy on computer users in Lebanon. It’s been dubbed Gauss (although Germanic-linguistic purists will no doubt be complaining that it should be written Gauß).
Gauss is a complex cyber-espionage toolkit, highly modular and supports new functions which can be deployed remotely by the operators in the form of plugins. The currently known plugins perform the following functions:
- Intercept browser cookies and passwords.
- Harvest and send system configuration data to attackers.
- Infect USB sticks with a data stealing module.
- List the content of the system drives and folders
- Steal credentials for various banking systems in the Middle East.
- Hijack account information for social network, email and IM accounts.
 The researchers at Russia-based Kasperky Labs who discovered it have christened it Gauss, and say it is aimed at pinching the pocketbooks of its intended targets, whoever they may be, by stealing account information of customers of certain banks in Lebanon, but also customers of Citibank and of PayPal.
The researchers at Russia-based Kasperky Labs who discovered it have christened it Gauss, and say it is aimed at pinching the pocketbooks of its intended targets, whoever they may be, by stealing account information of customers of certain banks in Lebanon, but also customers of Citibank and of PayPal.An analysis of the new malicious software shows it was designed to steal data from Lebanese lenders including the Bank of Beirut (BOB), BomBank and Byblos Bank, Kaspersky said. Gauss has infected 2,500 machines, while Flame hit about 700.
Two groups Russian-based Kaspersky Labs, which first published information on Gauss and Flame, and the Hungarian research lab Crysys are detecting the malware by looking for a font that shows up on infected machines called Palida Narrow.Roel Schouwenberg, senior researcher at Kaspersky Labs, said that researchers still don’t know why Gauss’s creators included the font file.
Have a look on relationship between Flame, Gauss, Stuxnet and Duqu:
One of the firm's top researchers said Gauss also contains a module known as "Godel" that may include a Stuxnet-like weapon for attacking industrial control systems. Kaspersky researchers said Gauss contained a “warhead” that seeks a very specific computer system with no Internet connection and installs itself only if it finds one.
*Image credit Kaspersky Lab
Have a look on relationship between Flame, Gauss, Stuxnet and Duqu:
One of the firm's top researchers said Gauss also contains a module known as "Godel" that may include a Stuxnet-like weapon for attacking industrial control systems. Kaspersky researchers said Gauss contained a “warhead” that seeks a very specific computer system with no Internet connection and installs itself only if it finds one.
*Image credit Kaspersky Lab
Zeus malware targeting BlackBerry and Android devices
Security researchers at Kaspersky Lab have discovered five new samples of the ZeuS-in-the-Mobile (ZitMo) malware package, targeting Android and BlackBerry devices.
Zitmo (Zeus in the mobile) is the name given to the mobile versions of Zeus, and it's been around for a couple of years already, mostly infecting Android phones. The Zitmo variant has reportedly been operating for at least two years targeting Android phones by masquerading as banking security application or security add-on.
ZitMo gets hold of banking information by intercepting all text messages and passing them on to attackers’ own devices. It gets onto devices inside malicious applications, which users are duped into downloading. In this case, the malicious app was posing as security software called ‘Zertifikat’.
Once installed, the packages forward all incoming SMS messages to one of two command and control numbers located in Sweden, with the aim of snaring secure codes and other data. Kaspersky found mobile users in Spain, Italy and Germany were targeted by these fresh variants, with two command and control (C&C) numbers found on Sweden’s Tele2 operator.
"The analysis of new Blackberry ZitMo files showed that there are no major changes. Virus writers finally fixed grammar mistake in the ‘App Instaled OK’ phrase, which is sent via SMS to C&C cell phone number when smartphone has been infected. Instead of ‘BLOCK ON’ or ‘BLOCK OFF’ commands (blocking or unblocking all incoming and outgoing calls) now there are ‘BLOCK’ and ‘UNBLOCK’ commands. Other commands which are received via SMS remain the same." Denis Maslennikov, a researcher at Kaspersky Lab.
The tactic is designed to help the criminals circumvent the out-of-band authentication systems used by many European banks, by hijacking the one-time password authentication password sent via SMS.
Earlier this year, Kaspersky warned of a set of malicious Android applications posing as security software. Zeus was sitting behind those apps, ready to siphon off text messages.
Mariposa botnet creator goes on trial
26-year-old Slovenian hacker known as Iserdo stands thought to have been behind the Mariposa botnet is on trial in Slovenia, charged with having masterminded an international cybercrime gang.
At its height, the Mariposa botnet infected up to 12.7 million PCs, with more than half of the Fortune 1,000 companies believed to have been compromised, including 40 major banks. Once a computer had been compromised and brought into the botnet, operators could steal information from innocent users - including credit card details and banking passwords.
Computer crime-fighting authorities had succeeded in bringing down the Mariposa botnet at the end of 2009, FBI officials worked with Spanish and Slovenian authorities to track down Mariposa's mastermind, Iserdo.
He was said to charge between $500 for basic versions of the botnet code and up to $1,300 for more advanced ones, which included customised features, such as capabilities which allowed its operators to to steal credit cards and online banking credentials.
 The code was even found to have infected 3,000 HTC handsets shipped by mobile operator Vodafone. Mariposa style botnets were built using Škorjanc's "Butterfly Bot" code, according to the Slovenian authorities, and it was sold to cyber criminals worldwide. Mariposa, the Spanish version of the botnet, was the largest and the most notorious.
The code was even found to have infected 3,000 HTC handsets shipped by mobile operator Vodafone. Mariposa style botnets were built using Škorjanc's "Butterfly Bot" code, according to the Slovenian authorities, and it was sold to cyber criminals worldwide. Mariposa, the Spanish version of the botnet, was the largest and the most notorious.Tuesday, August 7, 2012
Researcher demonstrate hardware based backdoor called Rakshasa
Security researcher Jonathan Brossard created a proof-of-concept hardware backdoor called Rakshasa that replaces a computer's BIOS (Basic Input Output System) and can compromise the operating system at boot time without leaving traces on the hard drive.

In short, firmware is software that is stored in non-volatile memory on a computer chip, and is used to initialise a piece of hardware’s functionality. In a PC, the BIOS is the most common example of firmware but in the case of wireless routers, a whole Linux operating system is stored in firmware.
Hardware backdoors are lethal for three reasons:
They can’t be removed by conventional means (antivirus, formatting).
They can circumvent other types of security (passwords, encrypted file systems).
They can be injected during manufacturing.

In short, firmware is software that is stored in non-volatile memory on a computer chip, and is used to initialise a piece of hardware’s functionality. In a PC, the BIOS is the most common example of firmware but in the case of wireless routers, a whole Linux operating system is stored in firmware.
Hardware backdoors are lethal for three reasons:
They can’t be removed by conventional means (antivirus, formatting).
They can circumvent other types of security (passwords, encrypted file systems).
They can be injected during manufacturing.
Rakshasa, named after a demon from the Hindu mythology, is not the first malware to target the BIOS the low-level motherboard firmware that initializes other hardware components. Rakshasa replaces the motherboard BIOS, but can also infect the PCI firmware of other peripheral devices like network cards or CD-ROMs, in order to achieve a high degree of redundancy.
Rakshasa can be installed by anyone with physical access to your hardware either at manufacturing time, or in the office with a USB stick. Fortunately, Brossard hasn’t released the code for Rakshasa but he seems fairly confident that other security groups/agencies have already developed similar tools.
Brossard built Rakshasa by combining several legitimate open-source software packages for altering firmware. Due to the efforts of programmers that have contributed to those projects, Rakshasa works on 230 different models of motherboard, says Brossard.
The only way to get rid of the malware is to shut down the computer and manually reflash every peripheral, a method that is impractical for most users because it requires specialized equipment and advanced knowledge.
Malicious Olympic 2012 Android Apps & Domains
Whenever an important event takes place, new opportunities for cyber criminals, especially for those who develop attacks based on social engineering, arise. Currently, the whole world has its eyes glued to TV screens watching the London 2012 Olympic Games.

Anti-malware and anti-virus solutions provider Webroot has issued a warning that an app app called "London Olympics Widget," which is described as an app that displays aggregated Olympic news coverage. In fact, it's really just harvesting the user's contact list and device ID while reading up on SMS messages too.
The package name is ‘com.games.London.Olympics.widget’. This app has a digital certificate claiming it was developed in New Delhi, India.
For this scam, cybercriminals create websites that are very appealing; some even look very professional that they make it seem that you are close to having access to live programming. Researchers explain that the crooks rely on black hat SEO techniques to make sure that their malicious websites show up among the first in search engine results.
The security firm has determined that close to 10,000 clicks have already been redirected to the fraudulent Olympics website.Overall, a number of 38,000 clicks have been redirected to such sites, the victims being spread out across 100 countries.
The official London 2012 mobile app can be downloaded from the site.

Anti-malware and anti-virus solutions provider Webroot has issued a warning that an app app called "London Olympics Widget," which is described as an app that displays aggregated Olympic news coverage. In fact, it's really just harvesting the user's contact list and device ID while reading up on SMS messages too.
The package name is ‘com.games.London.Olympics.widget’. This app has a digital certificate claiming it was developed in New Delhi, India.
For this scam, cybercriminals create websites that are very appealing; some even look very professional that they make it seem that you are close to having access to live programming. Researchers explain that the crooks rely on black hat SEO techniques to make sure that their malicious websites show up among the first in search engine results.
The security firm has determined that close to 10,000 clicks have already been redirected to the fraudulent Olympics website.Overall, a number of 38,000 clicks have been redirected to such sites, the victims being spread out across 100 countries.
Webroot advises that consumers should take a close look at the author of the app and then search the name to see if it is in fact a reputable company and/or developer, as seen in the photo above. A way that consumers can protect themselves from becoming a victim of these types of online scams is by learning about social engineering so they can recognize it and avoid falling into these traps .
The official London 2012 mobile app can be downloaded from the site.
Pakistani hackers deface Indian Southern Railways website

Website of the Southern Railways www.southernrailway.gov.in has been defaced apparently by Pakistani hackers.
The hacker group that calls itself 'Pak Cyber Pyrates' replaced the home page of the website with a page with content that denounces India's role in Kashmir.
Indian and Pakistani hacking groups are engaged in a cyber war of sorts with websites in both the countries being regularly attacked and defaced
Cortana scripting language introduced for Cobalt Strike and Armitage

At DEFCON 20, Raphael Mudge the developer of Armitage released the most significant update to Armitage. Armitage is now fully scriptable and capable of hosting bots in acollaborative hacking engagement.
Raphael Mudge is the founder of Strategic Cyber LLC, a Washington, DC based company that creates software for red teams. He created Armitage for Metasploit, the Sleep programming language, and the IRC client jIRCii. Previously, Raphael worked as a security researcher for the US Air Force, a penetration tester, and he even invented a grammar checker that was sold to Automattic.
Raphael talk about Cortana scripting language for Cobalt Strike and Armitage. Cortana allows you to write scripts that automate red team tasks and extend Armitage and Cobalt Strike with new features. This technology was funded byDARPA's Cyber Fast Track program and it's now open source.
Raphael talk about Cortana scripting language for Cobalt Strike and Armitage. Cortana allows you to write scripts that automate red team tasks and extend Armitage and Cobalt Strike with new features. This technology was funded byDARPA's Cyber Fast Track program and it's now open source.
Armitage a red team collaboration tool built on the Metasploit Framework. Cobalt Strike is Armitage’s commercial big brother. Both packages include a team server. Through this team server, multiple hackers may control compromised hosts and launch attacks through one instance of the Metasploit Framework.
Using Cortana, you may develop stand-alone bots that join your red team. Cortana bots scan hosts, launch exploits, and work on compromised hosts without stepping on each other or getting in the way of their human teammates.
Cortana scripts may also extend the Armitage and Cobalt Strike clients with new features. Cortana scripts can expose hidden Metasploit features, integrate third-party tools and agents, or control other Cortana bots.
LinkedIn Data breach costs $1 million

Business networking site LinkedIn has announced it took a hit of up to $1 million due to one of the year'slargest reported data breaches. LinkedIn spent between $500,000 and $1 million on forensic work after a large number of passwords were breached, LinkedIn CFO Steve Sordello said on the company's earnings call today.
He said the 175-million-member company continued to strengthen its website's security and is expected to add $2 million to $3 million in costs in the current quarter toward those efforts.
“Part of adding value to our members every day means ensuring that their experience on LinkedIn is safe and secure,” he said.“Since the breach, we have redoubled our efforts to ensure the safety of member account on LinkedIn by further improving password strengthening measures and enhancing the security of our infrastructure and data. The health of our network as measured by number of growth and engagement remains as strong as it was prior to the incident.”After the leak was discovered, LinkedIn reset the passwords of accounts that they believed were frozen.The stolen passwords were camouflaged using an outdated cryptographic hash function, SHA-1, created by the National Security Agency. In addition to this weakness, LinkedIn failed to add additional security layers, such as salting the passwords, a technique which randomly appends a string of characters.
Following the attack, LinkedIn confirmed in a blog post the addition of new security layers, including the salting of passwords.
“Part of adding value to our members every day means ensuring that their experience on LinkedIn is safe and secure,” he said.“Since the breach, we have redoubled our efforts to ensure the safety of member account on LinkedIn by further improving password strengthening measures and enhancing the security of our infrastructure and data. The health of our network as measured by number of growth and engagement remains as strong as it was prior to the incident.”After the leak was discovered, LinkedIn reset the passwords of accounts that they believed were frozen.The stolen passwords were camouflaged using an outdated cryptographic hash function, SHA-1, created by the National Security Agency. In addition to this weakness, LinkedIn failed to add additional security layers, such as salting the passwords, a technique which randomly appends a string of characters.
Following the attack, LinkedIn confirmed in a blog post the addition of new security layers, including the salting of passwords.
Fake Syria News Posted from Hacked Reuters blog and Twitter account

On Friday, Reuters blog platform was hacked with false posts and on Saturday, the @ReutersTech account on Twitter was taken over and renamed @TechMe. False tweets were sent before it was taken down.
The first attack came Friday after Syrian hackers loyal to President Bashar al-Assad allegedly gained access to Reuters’ blogging platform, which they used to post a fake interview with rebel Free Syrian Army (FSA) leader Riad al-Assad. The interview essentially said the general was withdrawing troops after a battle.Presumably, the same hackers are responsible for also compromising a Reuters Twitter account dedicated to technology news, which has about 17,500 followers. Reuters confirmed the breach today in a tweet on its main Twitter account:Earlier today @ReutersTech was hacked and changed to @ReutersME. The account has been suspended and is currently under investigationSeveral of the updates posted on the hacked Reuters account, which claimed that rebels in the city of Aleppo had been routed and were planning a tactical retreat, closely echoed details of the fabricated reports posted on the agency’s blogs two days earlier.
The tweets themselves were mostly pro-Syrian government messages, as well as some inflammatory statements targeted at the U.S. government.

One part of the elaborate fiction was an update reporting the fake news that President Obama had signed an “executive order banning any further investigation of 9/11.”

One part of the elaborate fiction was an update reporting the fake news that President Obama had signed an “executive order banning any further investigation of 9/11.”
No hacker collective has taken credit for this second breach, but still the main suspect remains the Syrian Electronic Army, a group known for heavily supporting the current government and aiding it in defending its infrastructures against hacktivists who oppose it.
Huawei and Cyber Espionage, a question of trust ?

Chinese telecoms equipment suppliers have previously been criticized for allegedly being security risks. Huawei is working with British spooks to prove that it has no backdoors in its products which would allow Chinese agents to snuffle Her Majesty's secrets.
Over the past ten years or so, Chinese telecoms firms such as Huawei and ZTE, another telecoms-equipment provider, have expanded from their vast home market to become global players. Huawei is becoming an increasingly powerful global player, capable of going head-to-head with the best in intensely competitive markets.Several big Chinese firms, including ZTE and China Mobile, a giant mobile operator, have attracted scrutiny. But thanks to its size and its international reach it is Huawei that gets most attention.
But according to the Economist, the centre is being used to persuade Q that equipment from the manufacturer that runs it can be trusted. GCHQ has a handy base near by. Apparenly anyone who is anyone is riding a cock horse to Banbury cross to see a Chinese company with a Western gloss.What is interesting is that Huawei staff have UK security clearances and some of them used to work for GCHQ, so the relationship in Blighty is very close.
Even Huawei suggests a proactive approach to security. “Believe no one and check everything,” says John Suffolk, former CIO of the British government and now Huawei’s global cyber-security officer. However, experts say that security flaws are difficult to find, and can sometimes be subtly embedded in the code, and possibly included by accident. As such, doubts remain.
The U.S. and Australia have made clear their distrust of one of the world’s biggest telecoms company. The Australian government, for instance, banned the company from participating in bids for its national broadband network due to potential spying threats. Huawei, which has grown to become one of today’s dominant telecommunications equipment companies, is likewise constantly under threat because of what some might call China-bashing.
Over the past ten years or so, Chinese telecoms firms such as Huawei and ZTE, another telecoms-equipment provider, have expanded from their vast home market to become global players. Huawei is becoming an increasingly powerful global player, capable of going head-to-head with the best in intensely competitive markets.Several big Chinese firms, including ZTE and China Mobile, a giant mobile operator, have attracted scrutiny. But thanks to its size and its international reach it is Huawei that gets most attention.
But according to the Economist, the centre is being used to persuade Q that equipment from the manufacturer that runs it can be trusted. GCHQ has a handy base near by. Apparenly anyone who is anyone is riding a cock horse to Banbury cross to see a Chinese company with a Western gloss.What is interesting is that Huawei staff have UK security clearances and some of them used to work for GCHQ, so the relationship in Blighty is very close.
Even Huawei suggests a proactive approach to security. “Believe no one and check everything,” says John Suffolk, former CIO of the British government and now Huawei’s global cyber-security officer. However, experts say that security flaws are difficult to find, and can sometimes be subtly embedded in the code, and possibly included by accident. As such, doubts remain.
Alleged Anonymous hacker arrested for Facebook threat

Hong Kongpolice said Sunday they had arrested a 21-year-old man believed to be a member of the international hacker group Anonymous, after he reportedly said on social networking site Facebook that he would hack several government websites.
“The Internet is not a virtual world of lawlessness,” a police spokesman said, adding that the man was required to report back to the police in October.
He faces up to five years imprisonment if found guilty.The man is a member of the global hacker group Anonymous, the South China Morning Post said. The group is said to have 20 members in the semi-autonomous Chinese territory, which guarantees civil liberties not seen on the mainland, including freedom of speech.
The police spokesman declined to confirm his link to Anonymous. The last posting on the “Anonymous HK” Facebook page on July 22 urged authorities to show “respect” to citizens.
Subscribe to:
Posts (Atom)